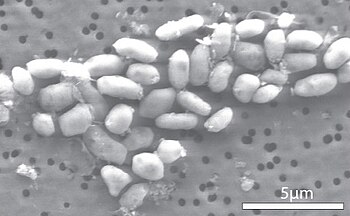
GFAJ-1 is a strain of rod-shaped bacterium in the family Halomonadaceae. The extremophile was isolated from the hypersaline and alkaline Mono Lake in eastern California, and reported as new to science by a research team led by NASA astrobiologist Felisa Wolfe-Simon in a 2010 Science journal publication. According to the authors, the microbe, when starved of phosphorus, is capable of substituting arsenic for a small percentage of its phosphorus and sustain its growth. Immediately after publication, other microbiologists and biochemists expressed doubt about this hypothesis, and the claim that this bacterium uses arsenic instead of phosphorus in its metabolism is robustly debated in the scientific community.

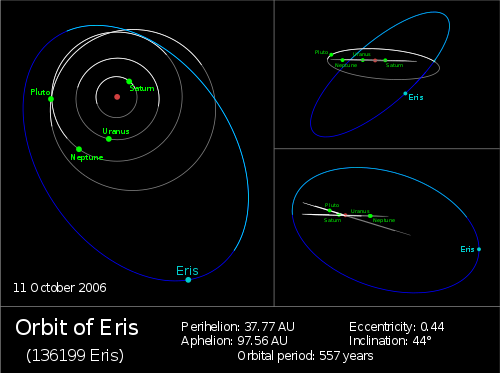
The GFAJ-1 bacterium was discovered by geomicrobiologist Felisa Wolfe-Simon, a NASA astrobiology fellow in residence at the US Geological Survey in Menlo Park, California. GFAJ stands for "Give Felisa a Job". The organism was isolated and cultured beginning in 2009 from samples she and her colleagues collected from sediments at the bottom of Mono Lake, California, U.S.A. Mono Lake is hypersaline (about 90 grams/liter) and highly alkaline (pH 9.8). It also has one of the highest natural concentrations of arsenic in the world (200 μM). The discovery was widely publicized on 2 December 2010.

Biochemistry
A phosphorus-free growth medium (which actually contained 3.1 ± 0.3 μM of residual phosphate, from impurities in reagents) was used to culture the bacteria in a regime of increasing exposure to arsenate; the initial level of 0.1 mM was eventually ramped up to 40 mM. Alternative media used for comparative experiments contained either high levels of phosphate (1.5 mM) with no arsenate, or had neither added phosphate nor added arsenate. It was observed that GFAJ-1 could grow through many doublings in cell numbers when cultured in either phosphate or arsenate media, but could not grow when placed in a medium of a similar composition to which neither phosphate nor arsenate was added. The phosphorus content of the arsenic-fed, phosphorus-starved bacteria (as measured by ICP-MS) was only 0.019 (± 0.001) % by dry weight, one thirtieth of that when grown in phosphate, and about one hundredth that of most bacteria. This phosphorus content was also only about one tenth of the cells' arsenic content (0.19 ± 0.25 % by dry weight). Other data from the same study obtained with nano-SIMS does however suggest a ~75-fold excess of phosphate (P) over arsenic (As) when expressed as P:C and As:C ratios, even in cells grown with arsenate and no added phosphate. When cultured in the arsenate solution, GFAJ-1 only grew 60% as fast as it did in phosphate solution. The phosphate-starved bacteria had an intracellular volume 1.5 times normal; the greater volume appeared to be associated with the appearance of large "vacuole-like regions".
When the researchers added isotope-labeled arsenate to the solution to track its distribution, they found that arsenic was present in the cellular fractions containing the bacteria's proteins, lipids and metabolites such as ATP, as well as its DNA and RNA. Nucleic acids from stationary phase cells starved of phosphorus were concentrated via five extractions (one with phenol, three with phenol-chloroform and one with chloroform extraction solvent), followed by ethanol precipitation. Although direct evidence of the incorporation of arsenic into biomolecules is still lacking, radioactivity measurements suggested that approximately one-tenth (11.0 ± 0.1 %) of the arsenic absorbed by these bacteria ended up in the fraction that contained the nucleic acids (DNA and RNA) and all other co-precipitated compounds not extracted by the previous treatments. A comparable control experiment with isotope-labeled phosphate was not performed.